Email marketing is big and an integral part of most businesses’ overall marketing strategy. 80% of business professionals believe that email marketing increases customer retention.
Therefore, due to the effectiveness of emails, marketers send email blasts frequently. Most of the marketers send their customers 3-5 emails per week.
However, with the rise of cybercrimes via emails, the need for cybersecurity has heightened. It was reported that 94% of malware was delivered by email.
There are constant email scams and email phishing that your consumers can become a victim of, as reports show that phishing emails are one of the top causes of ransomware attacks
Therefore, email marketers need to take extra cautionary/protective measures to ensure their marketing emails are greatly secured.
Marketing emails are the biggest target of hackers, because of their significance in generating revenue for businesses. They contain important customer and company information that makes both parties vulnerable to damages.
Below are the most typical threats that marketing emails are prone to but not limited to:
Spoofing
Spoofs are a dangerous threat that involves falsifying the real identity of an email sender to trick the recipient into taking actions that will put them at a disadvantage.
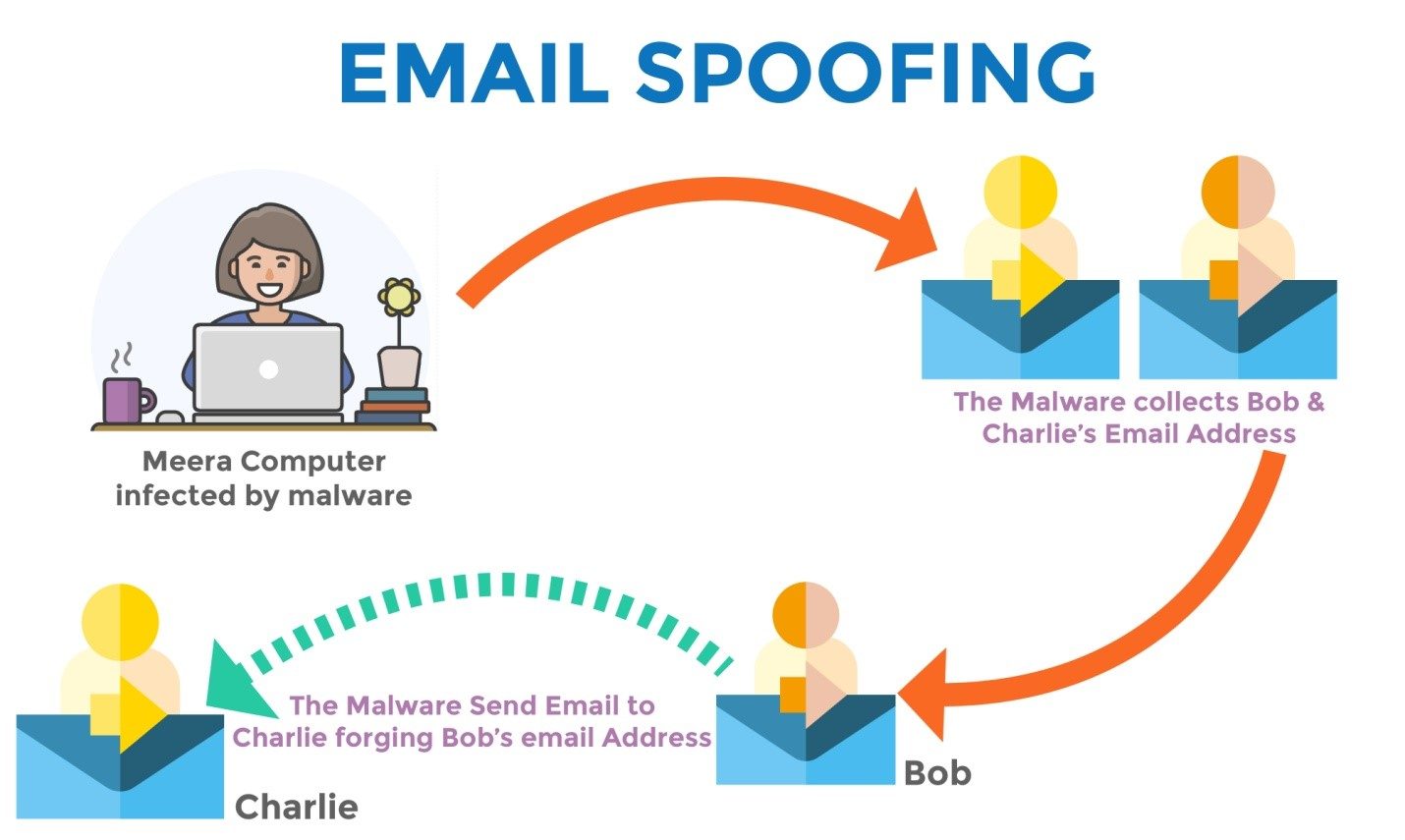
For example, cybercriminals will send emails in the guise of a real brand that the recipient might be familiar with, and they go ahead to deceive the victims to go on some website or reply with some sensitive information.
This will give the hacker a form of confidential information that should be limited to the company to gain inside access allowing them to launch several attacks.
Spoofing affects the reputation and images a brand has spent years building negatively.
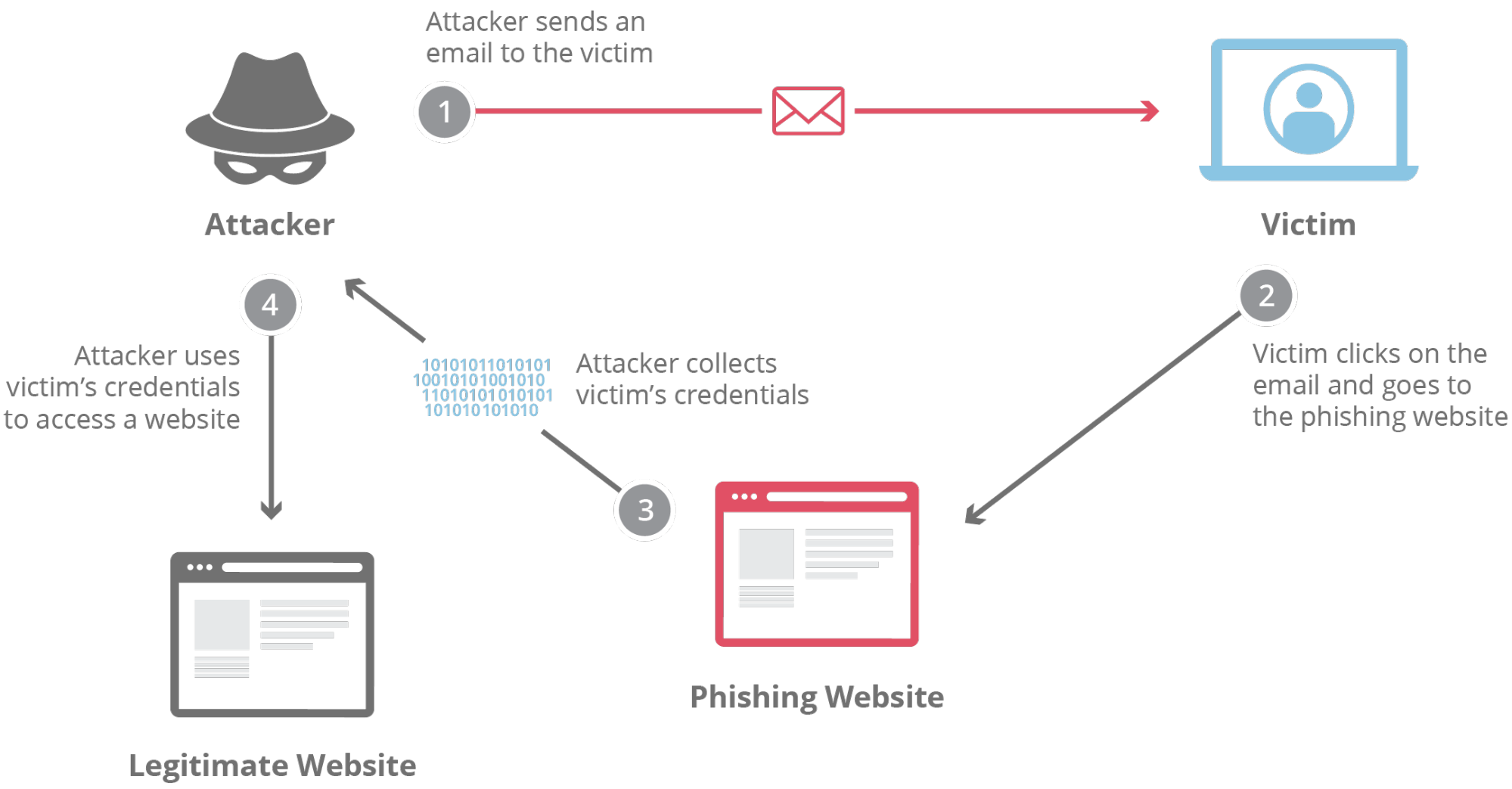
Phishing
Phishing threats are growing to become a great deal of concern for both email users and email marketers.
Because it wreaks a lot of havoc if successful, as cybercriminals take advantage of both personal and sensitive information to the detriment of consumers and companies.
For example, once they have consumer login information they can disguise themselves as clients or customers to penetrate your business and launch attacks that make your company vulnerable.
Scams
Email scams have for long been the nightmare of both email users and marketers. It is a frequent occurrence that doesn’t seem to slow down anytime soon.
In fact, cybercriminals have gotten smarter and innovative with their scamming schemes, that it is becoming harder not to fall for them.
This threat hurts email marketers’ campaigns because their email list recipients will lose their trust in them and no longer take them seriously.
This often leads to your marketing emails ending up in the spam folder and hurting your relationship with ISPs.
Also, email users are not the only ones on the receiving end of scamming activities, companies can also get scammed with hacked emails’ replies to their marketing emails.
Therefore, the need for taking necessary measures and having regulatory actions in place needs to be highly prioritized in the event of any suspicious activity.
Malware
Malware is inclusive of all types of sources or connections to software damages or system disruption like viruses, worms, Trojan horses, spyware, etc.
This is a very dangerous threat as it can lead to the destruction of your entire email marketing campaign because your systems will be hacked or corrupted.
And this will be very difficult to recover or rectify, so you want to do your very best to not become a victim of malware attacks.
Now that you have an idea of the types of threats you need to deal with as an email marketer, let’s discuss the email security best practices.
Email Security Best Practices
Here are 7 best security practices for email marketers:
1. Having Email Authentication Standards in Place
An email marketer needs to familiarize themselves with the email authentication standards available for enhanced email security.
Whether you are using transactional emails or curated content emails, these authentication standards give email marketers control over how their domain is used and a complete view of who is trying to attack their domain.
It gives email marketers the ability to secure their emails and instill confidence in recipients. Authentication standards make emails less prone to becoming victims of spam, spoofing, and phishing attacks.
Here are the top 3 email authentication standards you should put in place:
- Sender Policy Framework: This authentication standard allows a domain owner to indicate the email servers that are liable to send messages exclusively on the domain.
It is an IP-based solution that protects hackers from getting access to sending emails using the company’s email servers.
- DomainKeys Identified Mail (DKIM): This is an authentication standard that allows email recipients to verify the authenticity of the email cryptographically.
Your consumers can differentiate and identify your emails from spam ones through this authentication standard.
- Domain-based Message Authentication, Reporting, and Conformance (DMARC): The DMARC authentication standard allows Internet service providers (ISP) to easily avoid email scams that are domain-based.
It gives email marketers the control to indicate how emails were not authenticated using SPF or DKIM to be addressed.
This is the most secure authentication standard that has diverse functions to give you complete protection.
2. Use High-Quality Email Tools
The tool or system which you use to send out emails is critical to securing your marketing emails.
If the tool is prone to easy manipulation or infiltration then your emails are at risk of getting into the wrong hands.
For example, your ISP and cloud provider, how secure and trusted are they? Make critical research as to all the tools you intend to use.
The biggest mistake you will do is to opt for free options that provide little to no security, making a good investment will cost you less.
Because the damages of cyber-attacks are more costly. Therefore, develop a positive reputation with ESPs and domain servers to protect your marketing emails from vulnerabilities.
Tools like Wishpond offer the best security and email deliverability. It also offers you the option for easy integration with 300+ tools like Zapier, Salesforce, Slack, and others.
Need help with your next eCommerce email campaign?
Book a free call to learn how our team of marketing experts can help you create high converting email or social media contests today.
3. Employ the Use of Email Security Software
Don’t just stop at using a high-quality tool or software for your email marketing campaign, you need security software for those systems to be secure.
Having security software is no longer an option but a necessity for your email marketing campaign to protect your systems from cyber attacks.
Viruses, ransomware, malware, etc can come in various forms to disrupt your systems as mentioned earlier, and the absence of security software or tools will make you more susceptible to these malicious attacks.
Security tools will help you manage your data, protect your email from threats, encrypt your emails, and manage your passwords.
Therefore, invest in buying security software to help you fight off the spread of viruses on your systems.
There are various options for email security software, such as:
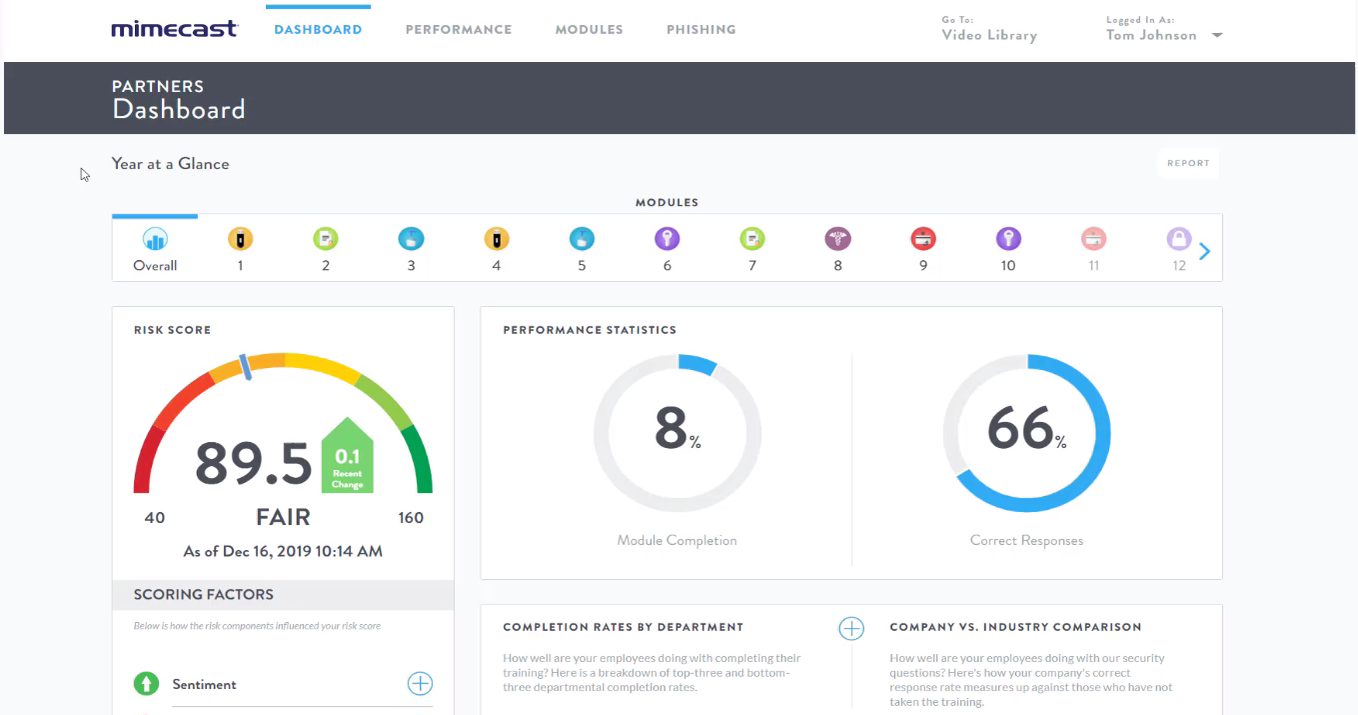
- Mimecast: It is a cloud based solution to block phishing attempts and upgrade your email security. Mimecast offers high-level email encryption and 99% spam rate detection. The pricing starts with $4 per user, per month.

NordPass: It offers an encrypted vault for storing all your complex passwords. NordPass password manager has a free version that lets you store unlimited passwords. With the premium subscription plan which starts with $1.49 per month, you can leverage features such as password sharing and use the software on six devices.
- PowerDMARC: It helps to boost your business reputation by preventing spoofed emails. Hackers might gain access to your email domain and start sending emails to your customers. Such phishing emails can compromise security and harm business reputation. PowerDMARC stops fake emails from being sent from your email domain and this secures your brand. The basic subscription is priced at $8 per month which offers protection for upto 5 domains.
4. Prioritize Email Encryption
Emails are not naturally secure and can be read by anyone that gains access to them, however, marketing emails contain important consumer details that can make them vulnerable if accessed by the wrong hands.
Therefore, you need to take an extra step to secure these emails to be read-only by the intended recipients by encrypting all your emails.
Reputable ISPs like Gmail, Yahoo, Outlook, etc don’t naturally have email end-to-end encryption, the alternative is employing a variety of methods to encrypt your marketing emails.
Here are 3 ways you can encrypt your marketing emails:
- Asymmetric Encryption: The concept of this approach is simple but difficult to use. It involves creating a public key to enable people to encrypt the messages they intend to send, then creating a private key exclusive to you for decryption. This means your email recipients need to have both keys for successful encryption. You can use a free software such as GnuPG to encrypt and sign your communications.
- Encryption in Transit: This method is popular amongst notable ISPs like Outlook, Gmail, etc. It involves encrypting emails whilst they are en route from one email server to the other. A mail server configuration recognized as Transport Layer Security is responsible for the journey based encryption. OpenSSL offers complete encryption for data in transit.
- Enterprise Email Encryption: This method allows you to encrypt emails through the active participation of your company. You get to encrypt emails by using email solutions software or applications. These applications can be cloud-based, or an extra hardware device. They allow you to send secure emails on both transit and servers. This method, though expensive, grants ease of use for both senders and recipients compared to the traditional encryption approach. Some of the best tools to use include Proofpoint.
5. Create Awareness
You can’t tackle what you don’t know. Let your consumers know that email scams are a thing to look out for. Spread awareness across your emails, through blogs, FAQs, etc.
Make your consumers understand the importance and graveness of email cyber crimes.
You can do the following to take active measures:
- Insert disclaimers as the footnotes in your emails, telling them how to identify spoofy and fake emails. For example, PayPal does this in their emails:
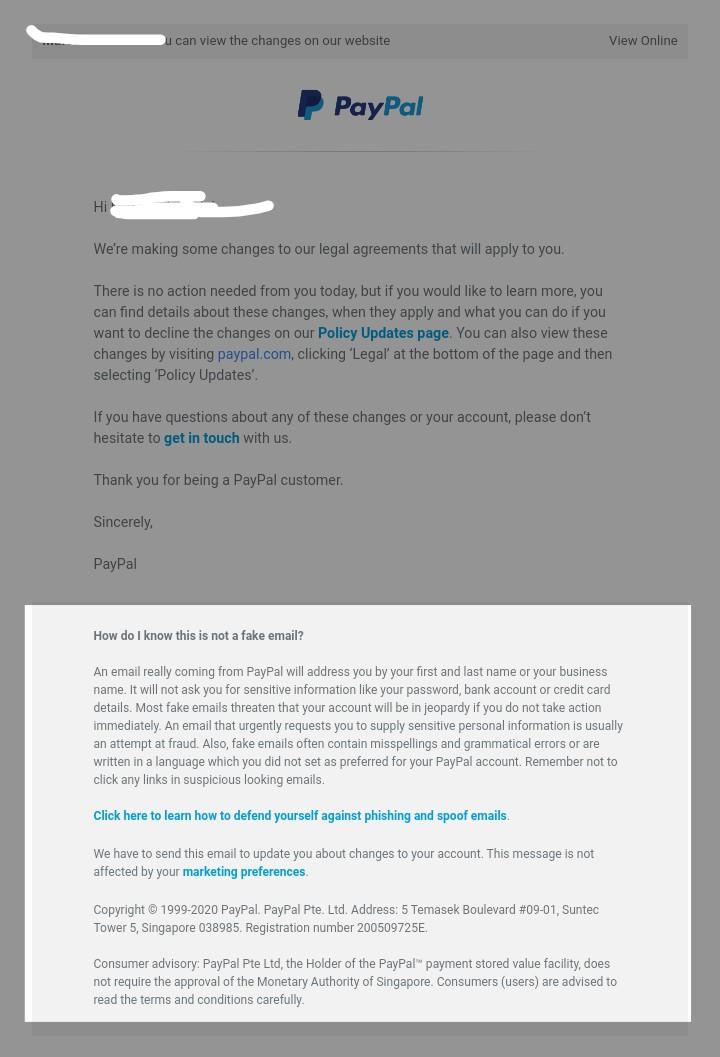
As you can see from the image above, PayPal highlighted the differences between a genuine email from them and a fake email from scammers.
- Create a page on your website that addresses the various types of email scams that your consumers are likely to encounter. Also, include the defensive measures they can take if they ever find themselves in such incidents.
Going back to PayPal, they further have a page on their site:
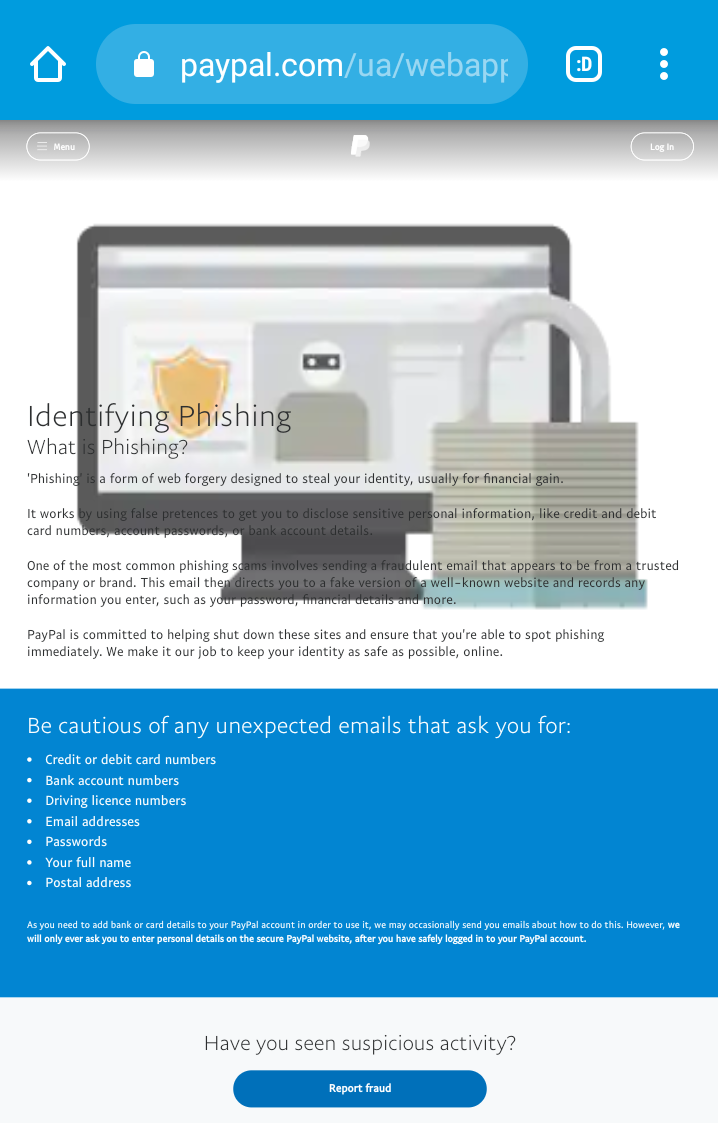
From the image above, PayPal pointed out what customers should look out for and gave them the option to report any sort of fraudulent activity.
A lot of email users report business emails as spams, therefore you have to curate your emails to look nothing like spam.
6. Adopt Top-notch and Secure Deliverability Practices
The way you deliver your emails plays a huge role in its security and protection from hackers.
You must adopt a secure system of delivering your emails, there should be a protocol in place that will track how emails are delivered.
Because when you send your emails, it passes through a lot of spam filters before reaching its recipients. It is at this stage that hackers try to exploit your emails, which is why reputable ISP providers employ advanced spam filtering processes.
Poor deliverability practices can make your emails end up in the spam folder, you need to take active measures to enable your emails to get tagged as the good one.
Here are actionable steps to adopt the best deliverability practices:
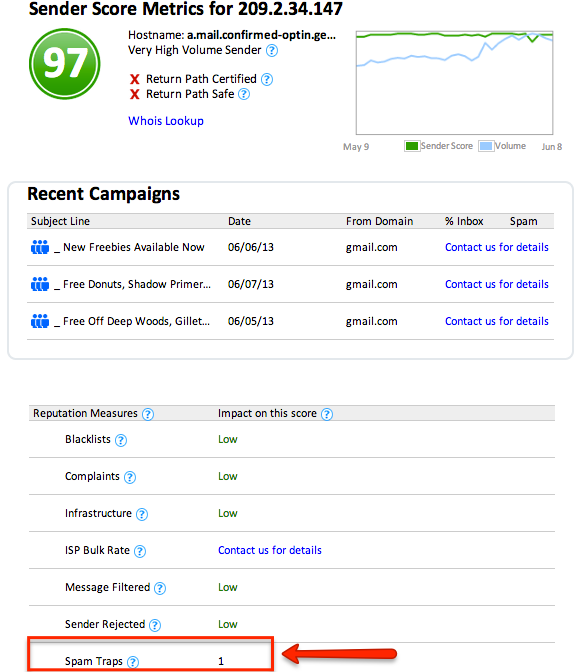
- Steer clear of spam traps: Spam traps are email addresses that ISPs and blacklist providers use to spot and block those who send emails to expired or unverified lists. Spam trap emails can affect your domain and make it vulnerable to hackers. Email marketers who buy email lists or don’t update their email lists are more prone to falling into spam traps.
Follow the different ways to avoid email blacklists. Also, ensure that you ask for people’s permission before sending them emails, you will be found guilty by ISPs. Take the help of email validation services like ZeroBounce that lets you avoid spam traps. To check whether your email domain is on a spam trap, find out your sender score. A score above 80 is great for sender reputation.
- Opt for a dedicated IP address: It’s preferable to use a dedicated IP address over a shared IP address to prevent complications from other email senders. Using a dedicated IP address gives you complete control over your emails which you can easily secure. You can ask your email service provider to give you a dedicated IP address.

- Be Law Compliant: Going back to the first step on getting permission from people, the best way to establish that is to establish an opt-in process to confirm their subscription. This way you can avoid getting just about any email address subscribed to your list and ensure compliance with the CAN-SPAM Act. Furthermore, you need an easy opt-out process to prevent any ISP complications due to complaints from subscribers.
7. Carry Out Routine Internal Checks
As an email marketer, you have to ensure you are leaving no stone unturned, look at your systems consistently to detect any form of vulnerabilities.
If you are working with a marketing team, take extra caution to keep your data safe and confidential.
Because most of the time, damages and breaches are caused from within, therefore, have a checklist that you should run from time to time internally to prevent breaches.
You should educate yourself on the major causes and roots of malware that you should be on guard for, you can regularly check in with your organization’s cybersecurity analyst/officer.
You can take the following active measures:
- Your business list of email addresses should be kept confidential with restricted access.
- Regularly scan for technical issues or viruses in your email software through the use of anti-virus software.
- Perform internal risk audits to assess your risk levels or vulnerabilities by rendering the services of an ethical hacker.
- Consistently clean out your email list to filter out spam trap email addresses.
Conclusion
Protecting your marketing emails from cybercriminals is very vital to protect your relationship with your consumers and your brand image. This is an essential email marketing KPI to manage.
These hackers are getting more innovative and strategic, therefore you need to be on guard at all times.
As email marketers, dealing with email security can be frustrating since you are required to not just focus on the marketing side of things but security too.
However, it doesn’t have to be overwhelming if you follow the best practices mentioned in this article, let’s do a quick recap:
- Having Email Authentication Standards in Place
- Use High-Quality Tools
- Employ the Use of Email Security Software
- Prioritize Email Encryption
- Create Awareness
- Adopt Top-notch and Secure Deliverability Practices
- Carry Out Routine Internal Checks
And there we have it, the best 7 email security practices for email marketers to protect their business and consumers.
Related Reading:
- The Complete Guide to Lead Segmentation
- Ultimate Email Deliverability Guide: 20 Ways to Improve Deliverability
- What is an Email Blast? How to Send Email Blasts (With Templates)
- 11 Email Marketing KPIs and Metrics You Should Be Tracking
- Email Bounce Backs – What Are They and How to Fix Them
- 7 Things To Test Before Sending An Email
- 6 Ways A No-Reply Email Address Hurts Your Business & How to Fix It
- 7 Five-Minute Email Marketing A/B Tests You Can Do Right Now
About the Author
 Joydeep Bhattacharya is a digital marketing evangelist and author of the SEO blog, SEOSandwitch.com. He has over 9 years of experience in helping businesses make the most of online marketing. Content writing is his passion and he is a regular contributor on sites like SEMrush, Ahrefs, Search Engine Watch, Smartinsights, and you can reach him via LinkedIn.
Joydeep Bhattacharya is a digital marketing evangelist and author of the SEO blog, SEOSandwitch.com. He has over 9 years of experience in helping businesses make the most of online marketing. Content writing is his passion and he is a regular contributor on sites like SEMrush, Ahrefs, Search Engine Watch, Smartinsights, and you can reach him via LinkedIn. -
amir

 Joydeep Bhattacharya is a digital marketing evangelist and author of the SEO blog,
Joydeep Bhattacharya is a digital marketing evangelist and author of the SEO blog,